BOSS Training Division
First steps
Lesson 1, the Caesar shift cipher and pattern detection
The simplest cipher, but a great introduction to both the implementation and cracking of a code.Powerpoint slides
Lesson 2, frequency analysis
Cracking substitution ciphers depends on finding hidden patterns in the text. Frequency analysis is your friend and is where the mathematics begins.Powerpoint slides
Lesson 3, the affine shift cipher
This is an introduction to modular arithmetic and builds on the first two lessons.Powerpoint slides
Lesson 4, breaking the affine shift cipher using modular inverses
A look at the mathematics behind the cipher, how to solve equations in modular arithmetic, and how that helps us break the affine shift cipher using inverses in modular arithmetic.Powerpoint slides
Lesson 5, the keyword cipher
Examines how to implement a much richer family of field ciphers based on an agreed keyword, and considers how to crack one in which the word structure is given, using cribs.Powerpoint slides
Lesson 6, cracking a keyword cipher using frequency analysis and cribs
This lesson takes what we know about frequency analysis and cribs and uses it to crack a much harder example of a keyword cipher in which the word structure is hidden.Powerpoint slides
The competition archivist, Madness, has written a couple of guides to cracking ciphers like the Vigenère and Batista which are based on the infamous tabula recta and its cousins. If you are ready to take the next steps in codebreaking this is a great place to start.
Head over to the BOSS Library if you want more like this.
Getting started with programming
Agent Thomas Campbell takes us through the steps he took to crack the Solitaire cipher from the Challenge in 2015, using Python: “It took me to places I hadn’t been before. I did things I wasn’t expecting to do …”
If you want more video, then head over to our Cinema!
Getting started with Python
One of our cipher challenge alumni wrote a great introduction to programming for anyone who, like Thomas, wants to take their skills to the next level. For the twentieth anniversary of the competition they have produced an all new version, focussed on Python. If you want to move beyond using a text editor and a spreadsheet to break codes then this is a great place to start!
If you would like to see what you can do with python and a web browser then take a look at our official codebreaking tools page for some examples!
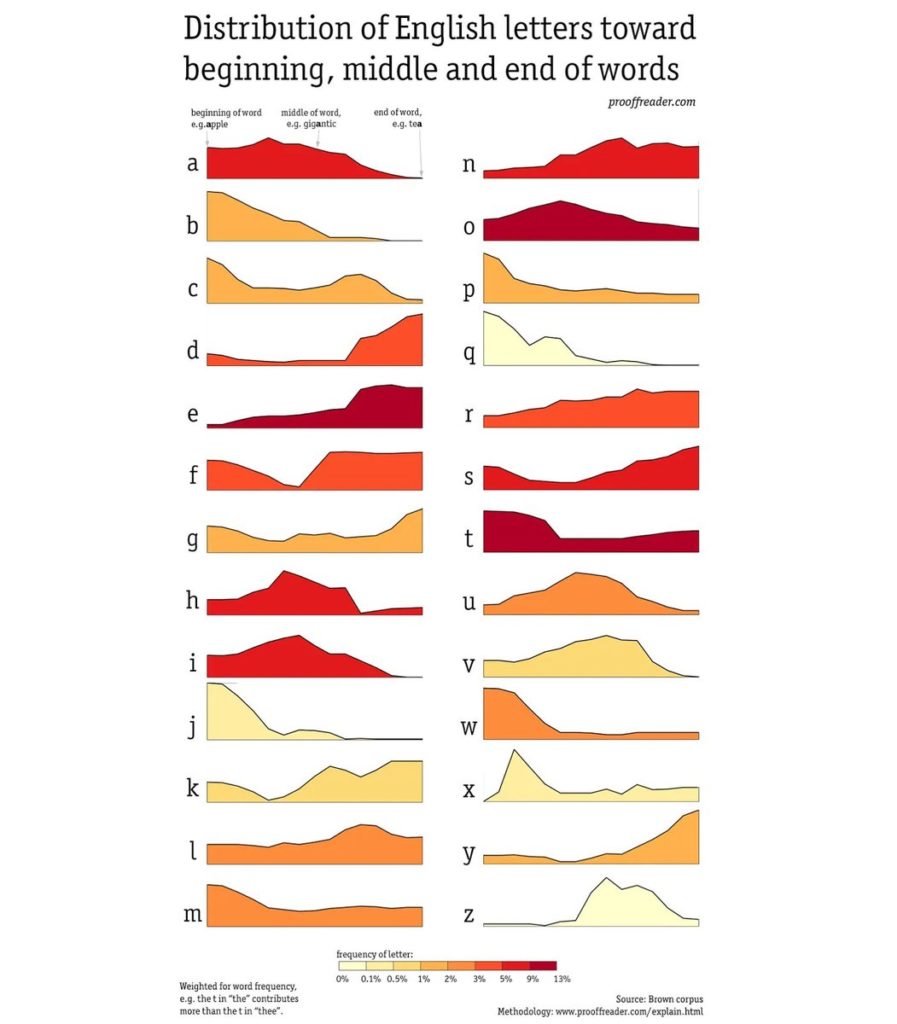
There are a number of statistical tools for analysing cipher text,(or tackling Wordle!) building on standard frequency analysis. This chart taken from @incunabula’s feed on Twitter might be useful, and in any case is certainly beautifully presented.
Advanced codebreaking
Some of the leading agents who worked on the 2016 case wrote up how they tackled it. If you are wondering what it takes to become an elite cryptanalyst at BOSS read how these agents tackled a message encrypted with a brand new code. A lot of the challenges you will face as a BOSS agent will not be anything like as difficult, but as for the later ones …
Notes from our debrief of Agent Cribbage, one of the team who broke open our 2018 case. Cribbage explains his thinking as he tackled another brand new code.Includes a nice brief introduction to the idea of the index of coincidence, one of the more sophisticated tools in the codebreaker’s toolkit.
A guide to solving Challenge 9B from the 2019 training module, written by Challenge archivist, Madness. He maintains an archive of all of the old challenge texts over on Github and if you search for them you will find them. He is also writing a long and interesting book about how to break the ciphers you see here and many more besides. Every time I look it has grown. If you ask nicely he might let you see it too.
Careers in cyber security
We work closely with a number of private organisations and government security agencies. If you are interested in a secondment with one of them, then take a look at their recruitment pages.
GCHQ have a number of technical roles which require strong mathematics skills, an enquiring mind and dedication. You can find out more about them here.

To anyone as old as Harry, Northrop Grumman are best known as the team that built the Lunar Module for the Apollo flights. They successfully landed 6 crews on the lunar surface and returned them to the safety of the Command Module after their missions. Even more impressively their engineers worked with NASA to bring back the crew of the doomed Apollo 13 mission, saving them from an awful death. Now NG are embarking on a new adventure, providing world class cyber security services.

The Institute of Mathematics and its Applications is a fabulous organisation that supports students and professional mathematicians across a range of careers in industry, business, government and academia.They also sponsor the National Cipher Challenge and they have a great website with loads of advice which is well worth a visit.